netstat is an essential tool for network issues diagnoses. for example, It prints OS network connections and list open ports, routing tables, interface statistics, masquerade connections. netstat comes in most Operating systems like Windows and Linux. however, in recent Linux releases it was superseded by other commands like ss and “IP” commands. Though, to unlock its full potentials, you have to use its parameter. in this article explain
netstat parameters
Admins usually use netstat to check specific things. therefore, they use its parameters to achieve that. however, if you execute netstat command without any parameters, it will print all active connections. keep in mind that ss command has replaced netstat without any parameter.
You can get all available parameters by typing –help or visit netstat manual, Instead, I will talk about the useful combination of parameters that comes with netstat. for that, the following table show number of parameter:
| –listening | -l | listen |
| –numeric | -n | numbers instead hostnames and service description |
| –program | -p | list program connecting on that port |
| –tcp | -t | TCP ports only |
| –udp | -u | UDP ports only |
| –version | -V | show netstat version |
| –route | -r | list routing table, the command ip route replaces it |
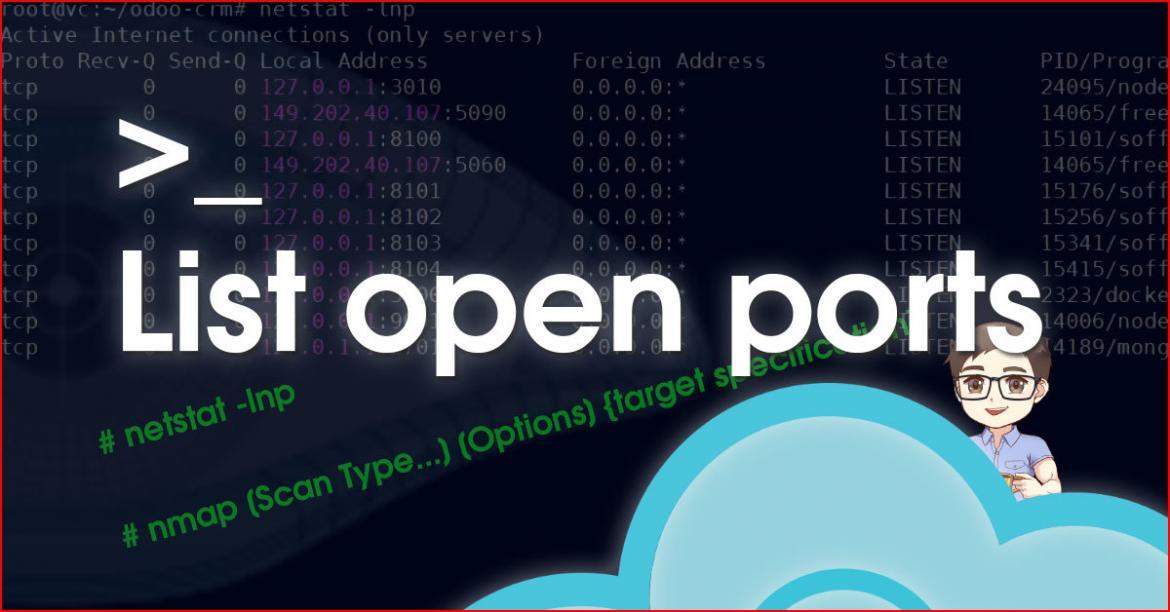
netstat list open ports on Linux.
To print Active ports that are listening to connections, in addition to the application responsible for opening the ports and their PID.
# netstat -lnp
Bellow, The output in order, the protocol, Recv-q, Send-Q, the Local listening port & Address, connected foreign port & address, the state of the port, and finally Process ID and Program name.

besides, You pipe netstat output into other commands like grep, egrep, or awk to filter the output. and search for a specific port or application.
to view information about a specific open port:
# netstat -lnp | grep ":<port number>"
or
The view information about a specific application and list the ports related to it.
# netstat -lnp | grep "<application Name>"
scan open ports using nmap tool.
Nmap is a port security network scanner. hence, it helps you to check servers’ firewall settings and security configurations. For example, to scan for open ports for specific server IP and list open ports
nmap –p– <Server IP>
To conclude, many applications open ports to communicate with remote resources. hence, to list the applications that are opening ports and listening for remote requests. For that, we used netstat that comes with Linux and windows to list the ports.